LLM-Augmented Tamper-Evident Secure Logging Framework
📑 10 slides
👁 22 views
📅 1/30/2026
Title Slide
Project title: LLM-Augmented Tamper-Evident Secure Logging Framework

2
Abstract
- Addresses log tampering and PII leakage using local LLM and Merkle chaining
- Novel integration of Phi-3 LLM for real-time anomaly detection
- Features PII masking, tamper-evident logs, and ntfy notifications
- Benefits: Enhanced security, privacy, and real-time monitoring

3
Introduction
- Secure logging is critical in AI/enterprise systems to prevent breaches
- Problem: Log tampering, PII exposure, lack of real-time detection
- Motivation: Incidents like SolarWinds highlight need for secure logs
- Overview: System ensures log integrity and privacy with AI analysis

4
Scope
- Included: Local deployment, real-time anomaly detection, PII masking
- Excluded: Cloud integration, multi-user auth, production scaling
- Focus on lightweight, local solution with AI-powered intelligence
- Notifications via ntfy for immediate alerting

5
Objectives
- Primary: Build tamper-evident logging with privacy and AI
- Implement Merkle-like chained hashing for integrity checks
- Integrate local Phi-3 LLM via Ollama for anomaly detection
- Provide real-time alerts and user-friendly React dashboard
6
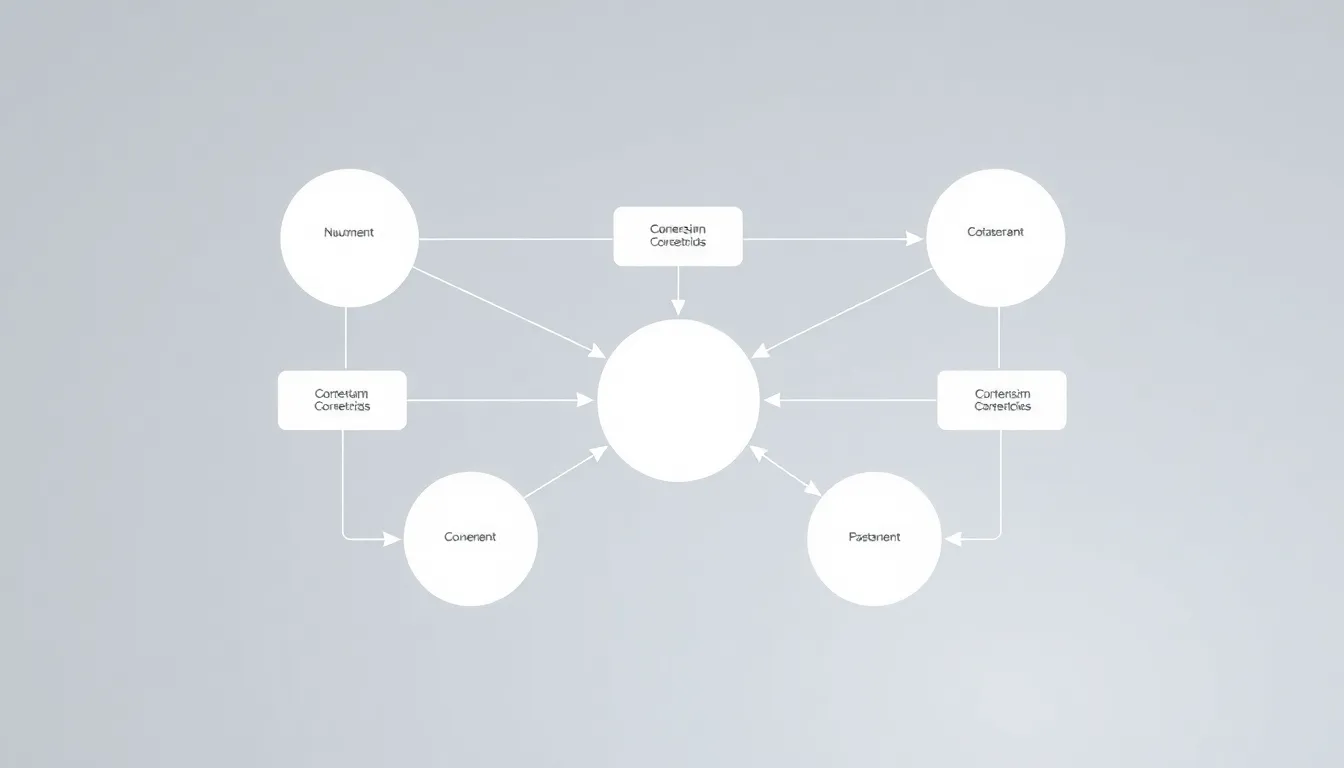
System Architecture
- Flow: User → React UI → FastAPI → PII Masking → LLM → Hashing
- Storage in SQLite with integrity verification via Merkle chaining
- Real-time alerts dispatched via ntfy.sh
- Trust boundaries clearly marked in data flow
7
Implementation
- Technologies: React, FastAPI, SQLite, Ollama, Docker, ntfy
- Steps: Setup Docker, build API, integrate LLM, add UI, notifications
- Key challenge: Ensuring low-latency LLM analysis for real-time logs
- Result: Containerized, scalable system with modular components
8
Modules
- Frontend: Dashboard, Logs, Alerts, ChainBanner, DemoButtons
- Backend: Ingestion API, Test Endpoints, ntfy Dispatch
- AI: Ollama + Phi-3 container for local processing
- Storage: SQLite logs table with hashed entries

9
Related Work
- Compared to ELK, Splunk, Acra - lacks local LLM and lightweight design
- Block-DEF uses heavy blockchain; our Merkle chaining is efficient
- SecureLLM requires cloud; our solution is fully local
- Novelty: Combines chaining, LLM, notifications in one system
10
Conclusion
- Achieved: Tamper-evident logs with PII protection and AI analysis
- Key benefits: Privacy, real-time alerts, local processing
- Future: Multi-node support, advanced LLM fine-tuning, RBAC
- Demonstrates viable alternative to cloud-dependent logging tools

1 / 10